ExeFilter - an open-source tool and framework to filter files and active content
ExeFilter is an open-source tool and python framework to filter file formats in e-mails, web pages or files. It detects many common file formats and can remove active content (scripts, macros, etc) according to a configurable policy.
Many networks are not really protected against active content which may enter up to the user workstation via e-mail, web or removable devices. Most of the common file formats such as Office documents, PDF, HTML or XML include native features which may be used to hide malicious active content or trigger XSRF and XSS attacks (see my articles about file formats security). A significant proportion of current attacks also take advantage of recent vulnerabilities discovered in various file formats to launch malicious code. The ever-increasing diversity and complexity of file formats make it hard to provide a comprehensive protection when using traditional methods such as antivirus engines and black-list filtering based on file extensions.
ExeFilter is an open-source tool and framework to improve protection against malicious active content in files. It has been designed to be either included in gateways (e-mail, web, web services, ...) or on user workstations to filter removable devices. Its unique white-list algorithm combined to a significant list of supported formats make it very effective to control which file formats are allowed to enter a secure network. It is also able to remove active content in order to receive only innocuous data.
Real-life example: malicious PDF files
Most of the malicious PDF files seen since 2008-2009 use native PDF features such as JavaScript or Launch actions to trigger their payload or to allow the exploitation of vulnerabilities. Since ExeFilter is able to clean PDF files by removing active content, it is effective against most of these malicious PDF files, even against zero-day exploits before they are discovered. See the following articles for more details:
- PDF exploits such as CVE-2009-4324
- The escape from PDF (CVE-2010-1240)
- Fighting PDF malware with ExeFilter (EUSecWest 2010)
Main Features
- Filter files according to a configurable white list policy: only allowed file types can go through.
- Unique filtering algorithm based on 1) file extension - 2) file contents - 3) active content detection and removal
- Recognizes the most common file formats: HTML, text, PDF, RTF, MS Word, Excel, Powerpoint, Project, Zip, JPEG, PNG, GIF, BMP, AVI, WAV, MP3.
- Can detect, remove or disable active content in some formats:
- HTML: JavaScript, VBScript, script URLs, Java applets, objects such as Flash, Iframes.
- PDF: JavaScript, Launch actions, Embedded files (effective against most current PDF malware, even zero-day exploits)
- MS Word/Excel/Powerpoint: VBA Macros, OLE Package objects
- RTF: OLE Package objects
- Recursive analysis of files into containers such as Zip.
- The output of the filter is only clean files with a recognized/allowed format, no active content, no executable file. The risk of launching malicious code is dramatically reduced.
- Can integrate antivirus engines such as ClamAV (clamd) or F-Prot for increased protection.
- Graphical User Interface
- Command-line interface
- Python API
- Can be integrated as a custom filter in Clearswift Mailsweeper
- optional logging (file, syslog) and archiving
- can generate HTML and XML reports
- Portable: runs at least on Windows, GNU/Linux and Mac OSX.
- Open-source license, GPL compatible.
Publications about ExeFilter
- Presentation at CanSecWest08: see attached file below.
- All CanSecWest08 presentations: http://cansecwest.com/csw08archive.html
- EUSecWest 2010 conference (June 2010): Fighting PDF malware with ExeFilter
- Fred Raynal's presentation about malicious PDF at hack.lu 2009 (ExeFilter is presented slides 34-39).
- Previous presentations in French about file formats security and ExeFilter are also available here.
News
- 2011-05-18: Portable ExeFilter can be run anywhere without installing anything
- 2011-05-01 v1.1.4-alpha4: added a new scan-only mode (both CLI and GUI)
- 2011-02-21 v1.1.4-alpha3: added a new GUI using wxPython
- 2010-09-12 v1.1.4-alpha1: improved PDF sanitization with Origami
- 2010-06-19 v1.1.3: new mini GUI, improved PDF sanitization with PDFiD
- 2010-02-24: version 1.1.2 published, see changelog for details.
- see also news on project website.
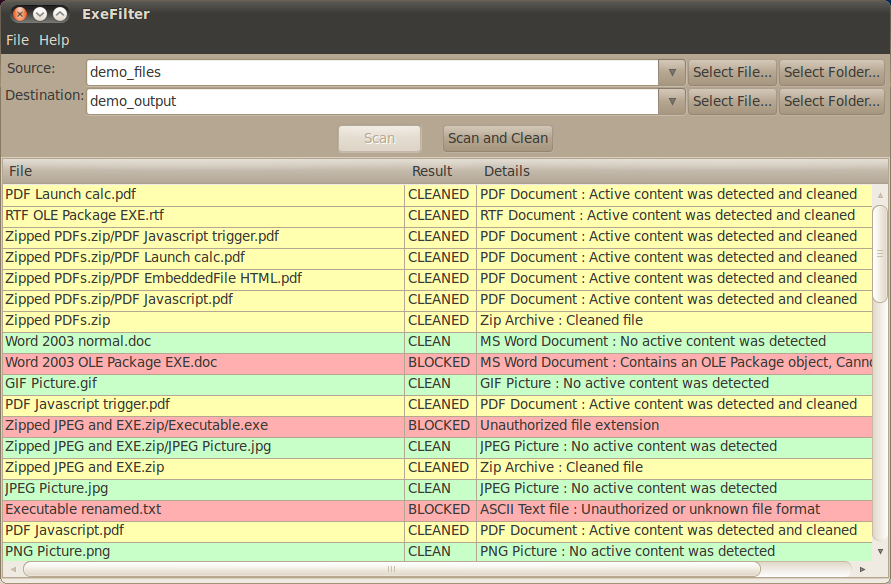
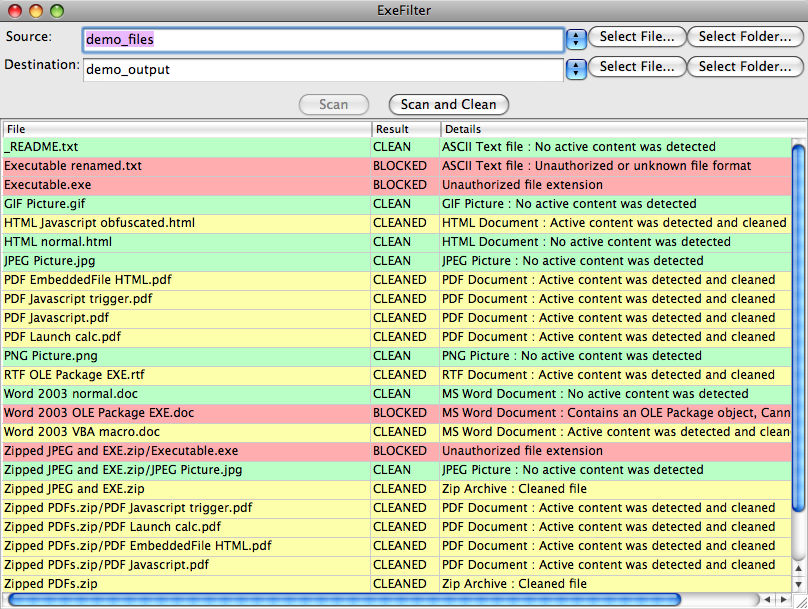
Screenshots
|
ExeFilter GUI on GNU/Linux Ubuntu |
ExeFilter GUI on Mac OSX |
Requirements
- Python 2.5, 2.6 or 2.7 (not 3.x yet)
- On Windows, pywin32 is required (Python for Windows extensions).
- wxPython for the new GUI
- Ruby for optimal PDF sanitization with the Origami engine
Download
- Download ExeFilter
- ExeFilter repository on GitHub
- Old ExeFilter project website (Adullact)
- Documentation
License
Cecill: open-source, GPL compatible.
Quick Demo
ExeFilter is provided with a few sample files located in the demo_files folder.
- Open each file in the demo_files folder, to look at active content (javascript, macros, embedded files, etc). Note: Some samples only work on Windows.
- If you have wxPython installed, just run ExeFilter_GUI.py, then click the "Scan and Clean" button.
- Else use the command line version in a shell:
- On Windows: simply run DEMO.bat, or type: ExeFilter.py demo_files -d demo_output
- On Unix/Linux/MacOSX: python ExeFilter.py demo_files -d demo_output
- Then open each file in demo_output, and compare results.
Sample usage
How to analyze one file (scan only mode):
| On Windows: |
ExeFilter.py <source file> |
| On Unix: |
python ExeFilter.py <source file> |
How to analyze one file and create a sanitized version (clean mode):
| On Windows: |
ExeFilter.py <source file> -o <destination file> |
| On Unix: |
python ExeFilter.py <source file> -o <destination file> |
Notes:
- It is possible to sanitize the file in place, by specifying the same path for source and destination.
- ExeFilter returns different errorlevel values according to the result (clean, cleaned, blocked or error - see documentation), which may be used to automate its usage in a gateway.
How to analyze all files from a directory according to the default policy, clean active content and copy sanitized files to a destination directory:
| On Windows: |
ExeFilter.py <source path> -d <destination path> |
| On Unix: |
python ExeFilter.py <source path> -d <destination path> |
Notes:
- Source path may be a directory, a single file, or a list of directories and files separated by spaces.
- Destination path must be a directory.
For example, in order to analyze all files from a CDROM or a USB stick on drive D: (on Windows) and copy a sanitized version in the directory C:\import, use the following command:
ExeFilter.py D:\ -d C:\import |
How to create a policy file with default options, and a HTML files describing each option:
ExeFilter.py -n policy.ini ExeFilter.py -e default_policy.html |
Then the policy.ini file may be edited using any text editor in order to modify options and filtering policy.
How to filter files using a custom policy:
ExeFilter.py <source path> -d <destination path> -p policy.ini |
For more information, see the current documentation.
How to contribute
Send an e-mail to decalage(at)laposte.net if you would like to contribute to the project, send patches, bug reports, develop new filters or simply tell us you have tested the tool on a specific platform.
| Attachment | Size |
|---|---|
| CanSecWest08_Lagadec_ExeFilter.pdf | 222.21 KB |

Comments
MS Office (docx, xslx, pptx)
Hi,
Does your tool provide support for MS office 2007 onwards, i.e. Open XML file formats?
Thanks!
MS Office 2007 formats (docx, xslx, pptx) are supported
Yes, Open XML formats are supported since version 1.1.4-alpha6. The documents are scanned and cleaned like zip files, allowing XML files and pictures inside (according to the configured policy). Any other binary file within the archive (e.g. macros) are stripped out.